Biba Integrity Model Ppt Powerpoint Presentation Outline Graphics Example Cpb | Presentation Graphics | Presentation PowerPoint Example | Slide Templates
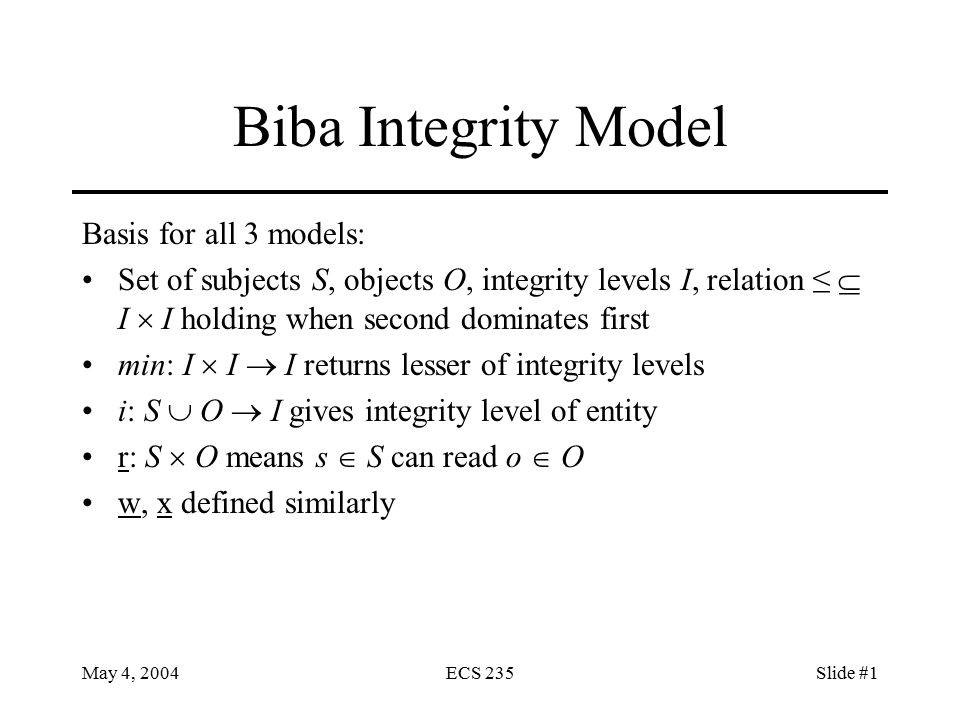
May 4, 2004ECS 235Slide #1 Biba Integrity Model Basis for all 3 models: Set of subjects S, objects O, integrity levels I, relation ≤ I I holding when. - ppt download

Improved Biba model based on trusted computing - Liu - 2015 - Security and Communication Networks - Wiley Online Library

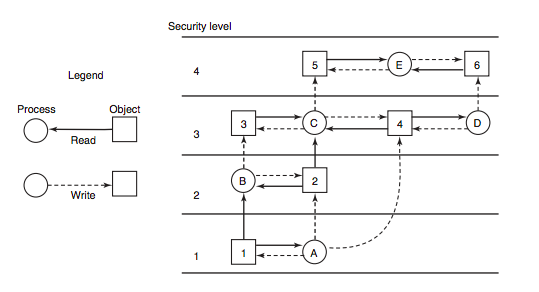
Two Laws of Biba Model The satisfaction of both Biba laws, prevents the... | Download Scientific Diagram
Evaluation of the Appropriateness of Trust Models to specify Defensive Computer Security Architectures for Physical Protection S